The ISO/IEC 27001 Lead Implementer course gives participants the knowledge and practical skills needed to implement, manage and continually improve an Information Security Management System (ISMS) in accordance with the requirements of ISO/IEC 27001. This internationally recognised course prepares you to support organisations in establishing robust information security practices that protect confidentiality, integrity and availability of critical information assets.
Over five intensive days, you will explore fundamental concepts and standards related to information security, and learn how to plan, implement, monitor and maintain an ISMS. The course combines theory with real-world application, case-based exercises and interactive discussions to ensure that participants can confidently apply ISO/IEC 27001 best practices in operational settings. It provides a solid foundation for professional roles in security governance and implementation, and leads directly to the Lead Implementer certification exam.
 Course objectives
Course objectivesAfter completing this course, participants will be able to:
 Prerequisites
PrerequisitesParticipants should have a fundamental understanding of ISO/IEC 27001 and general principles of ISMS implementation before attending this course.
 Target audience
Target audienceThis course is designed for managers, consultants, ISMS team members, expert advisers and others responsible for implementing or maintaining information security governance and compliance in organisations.
The course begins by introducing ISO/IEC 27001 and the Information Security Management System. Participants explore key standards, regulatory frameworks and core concepts that govern information security and set the foundation for implementation activities.
Participants learn how to plan an ISMS by analysing organisational context, defining scope, and establishing information security policies. Risk assessment techniques are introduced, and methods for developing Statements of Applicability and governance structures are explained.
This part of the course focuses on applying controls and policies, defining documentation and operational processes, and integrating information security practices into daily organisational routines. Communication, incident management and training plans are addressed.
Participants work with methods for monitoring, measuring and evaluating the effectiveness of the ISMS. Topics include internal audits, management review, treatment of nonconformities and strategies for continual improvement, as well as preparation for third-party certification audits.
The final stage is the certification exam day. Participants sit the exam and complete the course with a structured test environment and recap of key concepts.

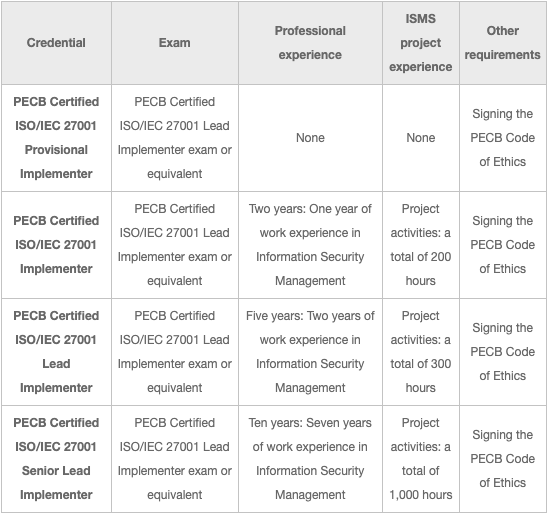
After successfully completing the exam, you can apply for the credentials shown on the table below. You will receive a certificate once you comply with all the requirements related to the selected credential. For more information about ISO/IEC 27001 certifications and the PECB certification process, please refer to the Certification Rules and Policies.
The exam is will take place at the end of the course on onsite classroom courses
For Virtual courses we will send out a voucher that gives you access to an online exam. This can be booked and taken home monitored by a proctor via camera. More information about the exam rules will be send fromPECB.
Test details:
As the exam is an Multiple Choice, candidates are authorized to use:
Examination rules and policies
Results will be communicated by email in a period of 6 to 8 weeks, after taking the exam. The results will not include the exact grade of the candidate, only a mention of pass or fail.
Candidates who successfully complete the examination will be able to apply for a certified scheme which is explained in the course description.
In the case of a failure, the results will be accompanied with the list of domains in which the candidate had failed to provide guidance for exams’ retake preparation.
Candidates, who disagree with the exam results, may file a complaint by writing to examination@pecb.com or through PECB ticketing system.
There is no limit on the number of times a candidate may retake an exam. However, there are some limitations in terms of allowed time-frame in between exam retakes, such as:
After the fourth attempt, a waiting period of 12 months from the last session date is required, in order for candidate to sit again for the same exam. Regular fee applies.
For the candidates that fail the exam in the 2nd retake, PECB recommends to attend an official training in order to be better prepared for the exam.
To arrange exam retakes (date, time, place, costs), the candidate needs to contact Glasspaper.

Duration: 5 days
Price: 27,900 NOK
Language: English
Format: Open course and corporate training
Hva lærer jeg på dette kurset?
Du lærer å implementere og forvalte et ISMS basert på ISO/IEC 27001, inkludert planlegging, risikovurdering, kontrollvalg og kontinuerlig forbedring.
Hva kreves for å delta?
Det kreves ikke at du har deltat på noen tidligere ISO foundation-kurs eller generelle ISO-kurs.
Du bør kun ha grunnleggende forståelse av ISO/IEC 27001 og prinsipper for informasjonssikkerhet før kurset.
Hvordan gjennomføres eksamen?
Eksamen gjennomføres enten fysisk på kursstedet eller online med voucher og online eksamensvakt.
Hva skjer hvis jeg ikke består første eksamen?
Du får vanligvis én gratis omtak, som bookes og tas online.
Får jeg ekstra tid på eksamen?
Du får en ekstra halvtime om engelsk ikke er ditt morsmål.
Hvilken sertifisering får jeg?
Etter godkjent eksamen oppnår du PECB Certified ISO/IEC 27001 Provisional implementer sertifiseringen. For å få full sertifisering kan det også stilles krav til dokumentert arbeidserfaring innen informasjonssikkerhet og ISMS-arbeid. Sjekk tabellen under sertifisering for mer informasjon.
Får jeg ISO-standaren?
Nei, men du får tilgang til en lånestandar som du kan bruke under kurset og eksamen.
Hva er forskjellen på Foundation, Implementer og Auditor?
Foundation, er gjennomgang av standarden direktivet eller loven. Implementer, rettet mot de som skal implementere en standard og etablere prosesser for etterlevelse. Auditor, rettet mot de som skal revidere et selskap i henhold til standarden, regelverket eller direktivet.
Hvem passer Lead Implementer best for sammenlignet med Lead Auditor?
Lead Implementer passer best for deg som skal jobbe operativt med å etablere og forbedre et ISMS i organisasjonen. Lead Auditor passer bedre for deg som skal gjennomføre interne eller eksterne revisjoner og vurdere etterlevelse av ISO/IEC 27001.
Er dette kurset relevant for ledere?
Ja, kurset er relevant for ledere, sikkerhetsansvarlige og konsulenter som jobber med implementering og styring av informasjonssikkerhet i organisasjoner.
Kan jeg ta dette kurset som e-læring eller selvstudie?
Ja, vi tilbyr kurset også som e-læringkurs. Du kan registrere deg på høre side.