ISO/IEC 27005 Risk Manager is a comprehensive course designed to give participants an in-depth understanding of information security risk management based on the ISO/IEC 27005 standard. The programme focuses on analysing, evaluating and managing risks through structured frameworks and methodologies, enabling organisations to make informed decisions about risk exposure and treatment.
«The trainer was the main reason I learned something valuable; made the class entertaining and fronted good discussions.»
This course provides participants with practical skills to conduct effective risk assessments, develop risk treatments and embed risk management practices into organisational processes. Through a combination of theory, case studies and practical exercises, participants learn how to identify threats and vulnerabilities, assess risk impact, and design appropriate control strategies that align with business goals and compliance requirements. The course also prepares delegates for the ISO/IEC 27005 Risk Manager certification exam.
 Course objectives
Course objectivesUpon completion of this course, participants will be able to:
 Prerequisites
PrerequisitesParticipants should have foundational knowledge of information security risk concepts, preferably through ISO/IEC 27005 Foundation or equivalent experience.
 Target audience
Target audienceThis course is suitable for risk professionals, information security practitioners, compliance officers, governance specialists, IT and security staff, consultants and anyone responsible for managing or coordinating risk activities within an organisation.
Participants start with a deeper exploration of risk theory, including key definitions, principles and the role of structured risk management within information security frameworks.
This section covers approaches for identifying and analysing risks, helping participants understand how to categorise and document threats, vulnerabilities, impacts and risk scenarios.
Participants learn methods for risk evaluation and prioritisation, including qualitative and quantitative techniques, risk scoring and how to interpret results to support decision-making.
This part of the course focuses on creating risk treatment strategies, selecting appropriate controls, and designing implementation plans that align with organisational objectives and compliance needs.
Participants explore how to integrate risk management practices across organisational governance models, including alignment with standards like ISO/IEC 27001 and other management systems.
This section covers how to monitor risk environments, evaluate effectiveness of treatments and embed mechanisms for continual improvement in risk practices.
The course concludes with guidance on the certification exam, covering exam structure, key topic review and exam-taking strategies.

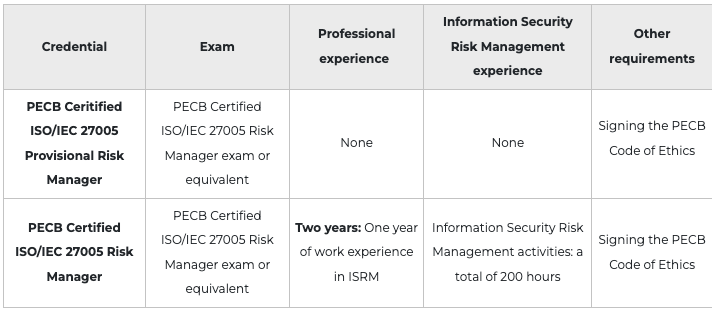
After successfully completing the exam, you can apply for the credentials shown on the table below. You will receive a certificate once you comply with all the requirements related to the selected credential. For more information about ISO/IEC 27001 certifications and the PECB certification process, please refer to the Certification Rules and Policies.
The exam is will take place at the end of the course on onsite classroom courses
For Virtual courses we will send out a voucher that gives you access to an online exam. This can be booked and taken home monitored by a proctor via camera. More information about the exam rules will be send from PECB
The exams an Multiple Choice exam; candidates are only authorized to use the following reference materials:

Duration: 3 days
Price: 20 900
Language: English
Format: Open course and corporate training
Hva lærer jeg på dette kurset?
Du lærer avanserte metoder for risikostyring i tråd med ISO/IEC 27005, inkludert identifikasjon, analyse, evaluering, behandling og kontrollvalg for risiko.
Hva kreves for å delta?
Det anbefales at du har grunnleggende kunnskap om informasjonssikkerhet og risikostyring, fortrinnsvis gjennom ISO/IEC 27005 Foundation eller relevant erfaring.
Hvordan gjennomføres eksamen?
Eksamen gjennomføres enten fysisk på kursstedet eller online med voucher og online eksamensvakt.
Hva skjer hvis jeg ikke består første eksamen?
Du får som regel ett nytt eksamensforsøk som tas online.
Får jeg ekstra tid på eksamen?
Ja, ekstra tid gis dersom engelsk ikke er ditt morsmål, i tråd med sertifiseringsreglene.
Hvilken sertifisering får jeg?
Etter godkjent eksamen oppnår du PECB Certified ISO/IEC 27005 Provisional Risk Manager sertifiseringen. For å få full sertifisering kan det også stilles krav til dokumentert arbeidserfaring innen informasjonssikkerhet og ISRM-arbeid. Sjekk tabellen under sertifisering for mer informasjon.
Får jeg ISO-standaren?
Nei, men du får tilgang til en lånestandar som du kan bruke under kurset og eksamen.
Hva er forskjellen på Risk Manager og Foundation?
Risk Manager fokuserer på avanserte risikoaktiviteter som analyse, evaluering og behandling, mens Foundation gir grunnleggende risikokonsepter.
Er dette kurset relevant for ledere?
Ja, kurset er relevant for ledere, risikokoordinatorer og fagpersoner som jobber med risikostyring og governance.
Kan jeg ta dette kurset som e-læring eller selvstudium?
Ja, dette kurset tilbys også som e-læring. Påmelding kan registreres på høyre side.